For a customer I’m migrating their legacy vSphere 5.5 environment to vSphere 6.5 U3.
The migration is from a windows vCenter to the VCSA.
First, we tried to use the GUI and stumbled over an issue.
GUI
The GUI, is of course a nice, friendly way to do this process. But when we got at the stage to select the size of the VCSA, we only had the ‘xlarge’ option.
And well… that was a bit too much. Because we were aiming at the ‘small’ size.
So we did some searching on the internet and found out that we were not alone. Although it was an encouraging thought, we still didn’t find what we were looking for.
Most of the threads and blog posts pointed to database size, log size etc..
And yes, they need to be checked. We had a vcenter database table of 7 million records, the size of the database was 80 GB. After some cleaning up and shrinking the database it was only a few GB.
But al this effort, didn’t persuade the GUI to give us the desired ‘small’ size option.
CLI
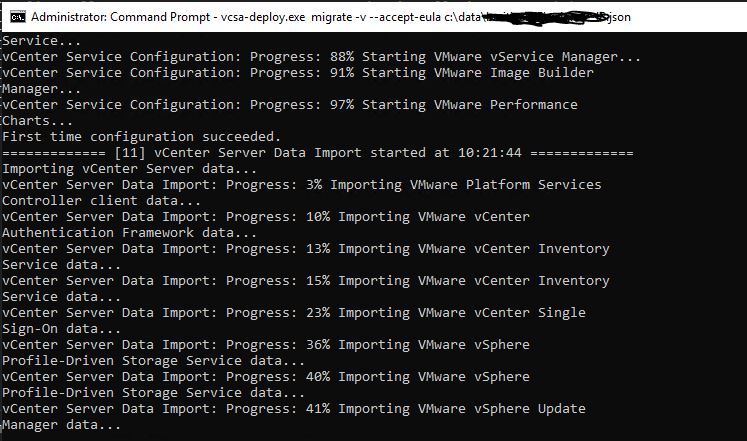
Hoping that the validation in the GUI was different than when using the CLI, we decided to migrate using the vcsa-deploy CLI method.
Yes, it involves creating a json file. But the .iso file for the vcsa contains several template files, for several migration scenarios.
We used on of the templates, customized it to our needs (setting the size to ‘small’. And after some trial and error we finally got it working.
TIP: validate your json file with
vcsa-deploy --precheck-only \some_path_to_json_file\migrate.jsonIf you want to read more about the CLI way of migration, check the vmware docs here.
vcsa-deploy creates for every run a new log folder . When we checked the logs we found out that vcsa-deploy was content with the ‘small’ size option we configured in the json file.
Thoughts
Why not 6.7 U3, well due to dependencies 6.5 U3 is at the moment the most current version we can run.
Although this post is about migrating to 6.5 U3, it could also work for 6.7 U3, but no guarantees.
The gist of this all is, if the GUI doesn’t work, try doing it the CLI way.
